
Ideal Data Memory
The 21st century is the age of information. More and more data are generated on the daily basis creating an ever-increasing demand for storage space. Not every home computer, let alone a mobile device, can store all its own generated data. The capacity of the built-in memory is growing along with requirements for data safety. The increased volume of generated data proportionally increases the number of potential threats to the storage of this data
With the growth in the number of devices, cloud storage services are becoming increasingly important. Many cloud storage providers promise fast, reliable and convenient services. However, the things are a bit more complicated.
The year 2013 was marked by a scandal involving the outdated SSL service certificate by Microsoft Azure which provided criminals with an opportunity to hack the Xbox Live system;
The so-called Celebgate incident, which happened in 2015, when hackers stole intimate photos of some celebrities from the iCloud (Apple) cloud storage;
The number of hacks inflicted on cloud services is growing every year at the rate around 50%;
Approximately 70% of companies have at least one application running in a cloud;
Lloyd's of London and Cyence believe that a massive attack on cloud storage can cause losses in excess of $ 5 billion, and only 15-17% of the total amount will be covered by insurance;
In 2017, the data storage of Equifax, the US leading consumer credit report agency, had been hacked resulting a personal data loss of 143 million customers. Consequently, the value of company's stocks has plummeted by 13%;
The absence of two-factor authentication resulted in a personal data theft of 80 million customers of Anthem, an American health insurance company.
Countermeasures to emerging threats
- The encryption of data by the user could be a viable method of countering cyber-attacks and potential data theft;
- Another way is to select an additional option offered by cloud service, which provides uploaded data to be encrypted by the service;
- The two-factor authentication (2FA) allows to increase the level of data access protection with minimum costs; 4. An anti-virus software which is a more conservative method of data protection.
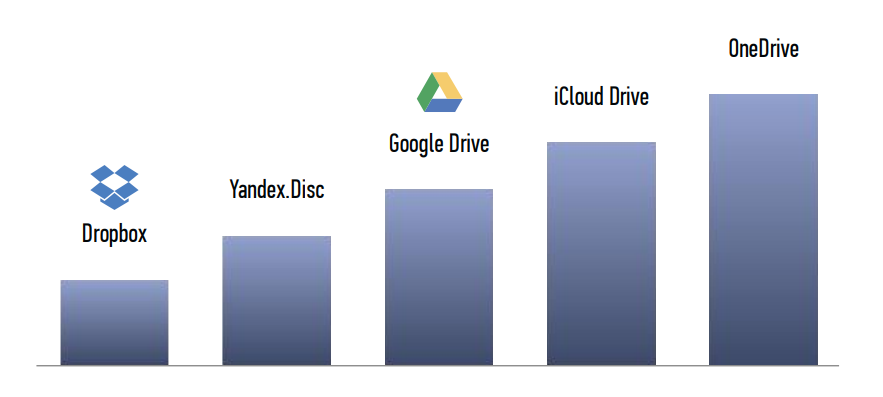
Safety rating of popular cloud storage services
The world-famous company UBER was subjected to a massive cyber attack, as a result, the data of 57 million drivers and customers had been stolen.
The most disturbing thing was covering by the company the very fact of hacking and theft, and the payment to the perpetrators a ransom of $ 100 thousand dollars. The attack was interesting in itself because hackers got access to the company's data through the GitHub service, where they hacked several accounts, downloaded data from Uber employees and with this data accessed a huge array of Uber data in the Amazon Web Services used by Uber for calculations.
Several years earlier, Yahoo and Equifax were hacked, along with many other companies and private accounts.
The need for the guaranteed security of stored documents
Currently, there isn't a single data storage on the market that can guarantee the absolute security of the documents that have special value and, at the same time, is accessible for the ordinary people
- The consumers have the demand for secure storage of their personal and classified documents of particular importance
- IDM introduces the service that can boast the superior level of security which is way higher than the one offered by any of the similar providers on the market and exceeds all State standards regarding the secure data storage
- Despite the fact that almost all State services have the highest level of data protection, they also experience the leak of data
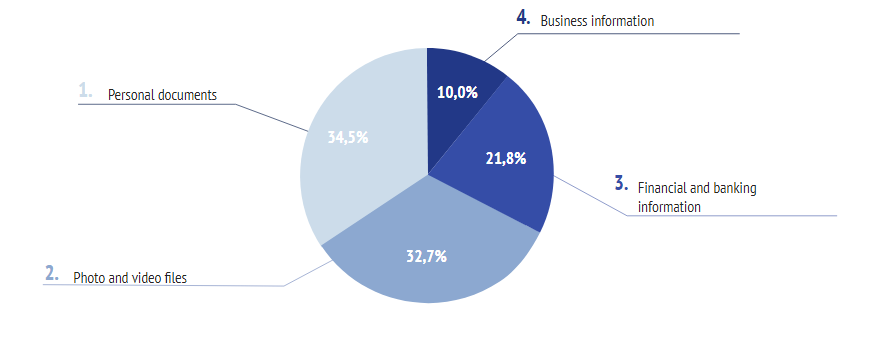
Types of data that requires superbly secure storage:
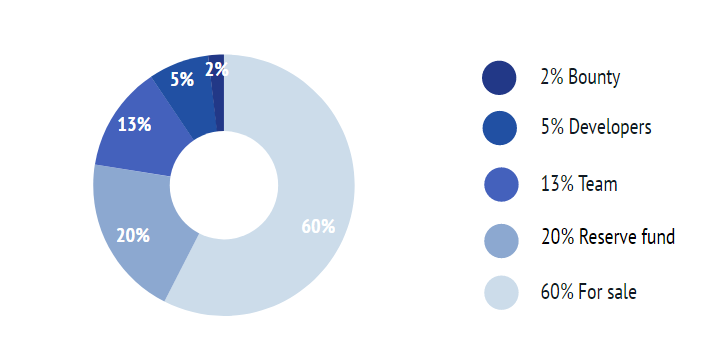
Token Distribution
Project team


author: koteb17
Tidak ada komentar:
Posting Komentar